Sign in to get started.
See and share your earned badges
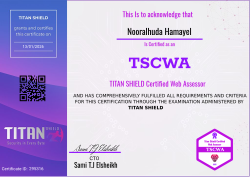
TITAN SHIELD Certified Web Assessor
- 1 Download the badge image (see below)
- 2 Now copy the badge link to make sure it links to your badge
- 3
- 4 Open Gmail and click on Settings -> See all settings
- 5 Scroll down to the Signature section
- 6 Click Insert Image > Upload image
- 7 Click on the badge image and resize it
- 8 Select the image and click on the link icon
- 9 Past the badge URL link in the Web address box
- 10 Click save to finish
- 1 Download the badge image (see below)
- 2 Now copy the badge link to make sure it links to your badge
-
3
- 4 Open Outlook and click on Home Tab -> New Email -> Signatures
- 5 Add a New Signature or edit an existing one
- 6 Select the Image icon in the toolbar
- 7 Insert the image downloaded into your signature
- 8 Select the image and click on the link icon
- 9 Past the badge URL link in the Web address box
- 10 Click save to finish
TITAN SHIELD CERTIFIED WEB ASSESSOR
TSCWA-100: Web Penetration Testing & Red Team Operations
The Titan Shield Certified Web Assessor (TSCWA-100) is an elite, immersive training initiative designed to forge the next generation of offensive security professionals. Aligned with OWASP (Open Web Application Security Project) standards and industry best practices, this intensive certification program transforms candidates into highly skilled web penetration testers and red team operators through real-world scenarios, structured methodologies, and hands-on exploitation techniques.
PROGRAM STRUCTURE
1. Foundational Security Theory
- Deep dive into network protocols (TCP/IP, HTTP/S, DNS, SSL/TLS)
- Web application architectures and session management
- Authentication and authorization mechanisms (OAuth, JWT, SAML)
- OWASP Top 10 vulnerabilities and emerging threat vectors
- Secure coding principles and defensive measures
2. Applied Laboratory Training
- Controlled environments simulating real-world vulnerable applications
- Progressive exercises in reconnaissance, enumeration, and exploitation
- Vulnerability analysis across CVSS-rated security flaws
- Exploitation frameworks and payload development
- Post-exploitation techniques and evidence collection
3. Red Team Operations
- Multi-phase adversarial simulation exercises
- Team-based coordinated attacks against hardened targets
- Operational security (OPSEC) and stealth techniques
- Adaptive threat modeling and evasion strategies
- Chain exploitation and advanced persistence mechanisms
4. Professional Assessment & Certification
- Technical competency examinations
- Peer-led security reviews and knowledge transfer sessions
- Mentor-supervised capstone projects
- Comprehensive performance evaluations
- TSCWA-100 certification upon successful completion
CORE COMPETENCIES DEVELOPED
Information Gathering & Reconnaissance
- Open-Source Intelligence (OSINT) collection and analysis
- Passive reconnaissance via search engines, DNS records, and public databases
- Active scanning with Nmap, Netdiscover, and Masscan
- Service enumeration and version detection
- Attack surface mapping and target profiling
Web Application Penetration Testing (OWASP-Aligned)
- Manual vulnerability assessment methodologies
- Automated scanning with Burp Suite Professional and OWASP ZAP
- OWASP Top 10 Exploitation:
- Injection attacks (SQL, NoSQL, LDAP, OS Command)
- Broken authentication and session management
- Cross-Site Scripting (XSS): Reflected, Stored, DOM-based
- Cross-Site Request Forgery (CSRF)
- Insecure Direct Object References (IDOR)
- Security misconfigurations and XXE attacks
- Sensitive data exposure and improper access controls
- Web Application Firewall (WAF) bypass techniques
- Custom payload crafting and encoding strategies
- API security testing (REST, SOAP, GraphQL)
Post-Exploitation & Persistence
- Windows and Linux privilege escalation techniques
- Credential harvesting and hash cracking
- Command & Control (C2) infrastructure deployment
- Maintaining persistent access and backdoor implementation
- Defensive tool evasion and anti-forensics
- Secure data exfiltration methods
Professional Reporting & Communication
- Risk-based vulnerability classification (CVSS scoring)
- Technical findings documentation with proof-of-concept
- Executive-level summary reports for stakeholders
- Remediation recommendations aligned with industry frameworks
- Presentation skills and client-facing communication
- Responsible disclosure practices
Industry-Standard Toolset Mastery
- Exploitation Frameworks: Metasploit, Cobalt Strike, Empire
- Vulnerability Scanners: Nessus, OpenVAS, Nikto
- Password Attacks: Hydra, John the Ripper, Hashcat
- Web Proxies: Burp Suite, OWASP ZAP, Fiddler
- Scripting & Automation: Python, Bash, PowerShell
- Collaboration Tools: Git, Markdown documentation, ticketing systems
CERTIFICATION OUTCOMES
Upon successful completion of the TSCWA-100 Program, certified professionals will possess:
- Titan Shield Certified Web Assessor (TSCWA-100) credential
- Comprehensive understanding of offensive security methodologies
- Practical expertise in web application and network penetration testing
- Proficiency with industry-leading security assessment tools
- Real-world experience through simulated red team operations
- Professional reporting and communication capabilities
- OWASP-aligned testing framework knowledge
- Readiness for roles in penetration testing, red teaming, and security consulting
CERTIFICATION DETAILS
Credential: Titan Shield Certified Web Assessor
Code: TSCWA-100
Duration: 3 Months Intensive hands-on program
Prerequisites: Foundational IT/security knowledge recommended
Assessment: Practical labs, technical exams, and capstone project
Age & Background
- Be at least 18 years of age.
Hold a high-school diploma or equivalent (or higher).
Program Completion
- Successfully complete the Titan Shield Certified Web Assessor (TSCWA-100) Internship Program with a focus on Web Penetration Testing (minimum 230 hours of combined theory, labs, and red-team exercises).
Assessment Requirements
- Achieve a passing score of 80% or above on the written examination covering core concepts (network protocols, web architectures, threat modeling, etc.).
- Demonstrate practical skills by completing a hands-on penetration testing scenario under supervised conditions, with all critical findings identified and remediations documented.
Ethics & Conduct
- Sign and adhere to Titan Shield’s Code of Ethical Hacking and non-disclosure agreement.
- Maintain professional conduct throughout all training and examination activities.
Documentation & Review
- Submit a concise technical report summarizing one mock pentest engagement, including executive summary, risk ratings, and remediation roadmap.
- Receive a satisfactory performance review from a Titan Shield mentor.
| Blockchain Badge Image | |
| Registration: | 13/01/2026 15:40 |
| File: | Badge Image |
| File hash: | 2a9a3fa89e608c1d3b9ca7a2e68db204f023106ba2c24c9edc149339a70d12e8 |
| Block hash: | 0000000000000000000104ee3a737af3b6d92c27d8a8e51e477472ebdfc68a8c |
| Transaction: | e0a5a5a014c0db27e9ddcb0707e78eb83e88c25b9374e4cf246bdc4a84f1fd1b |
| Blockchain Certificate Image | |
| Registration: | 13/01/2026 15:40 |
| File: | Certificate Image |
| File hash: | 3a5d86ab917ab9f56d5eaebf53b9416c9da49a48014e2632caf6e59e6cdb2f3a |
| Block hash: | 0000000000000000000104ee3a737af3b6d92c27d8a8e51e477472ebdfc68a8c |
| Transaction: | e0a5a5a014c0db27e9ddcb0707e78eb83e88c25b9374e4cf246bdc4a84f1fd1b |
| Blockchain Certificate PDF | |
| Registration: | 13/01/2026 15:40 |
| File: | Certificate PDF |
| File hash: | 08869ef5724f629e75cd675639e58091ad42934fc7019f621443bac79020e8d0 |
| Block hash: | 0000000000000000000104ee3a737af3b6d92c27d8a8e51e477472ebdfc68a8c |
| Transaction: | e0a5a5a014c0db27e9ddcb0707e78eb83e88c25b9374e4cf246bdc4a84f1fd1b |